Insights

Phishing: What It Is, How to Detect It, and How to Protect Yourself from Cyberattacks
-Phishing remains one of the main cyber threats in 2025. Despite advances in cybersecurity, cybercriminals continuously perfect their techniques to deceive users and companies. In this article, we explore what phishing is, how it has evolved, the types that exist, and how you can protect yourself from these attacks.
What is phishing?
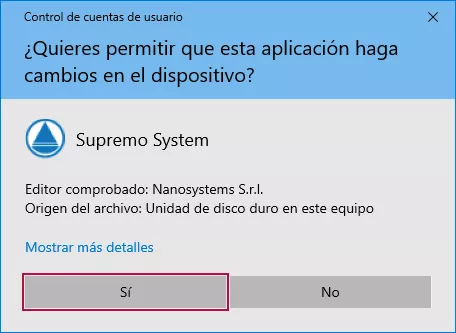
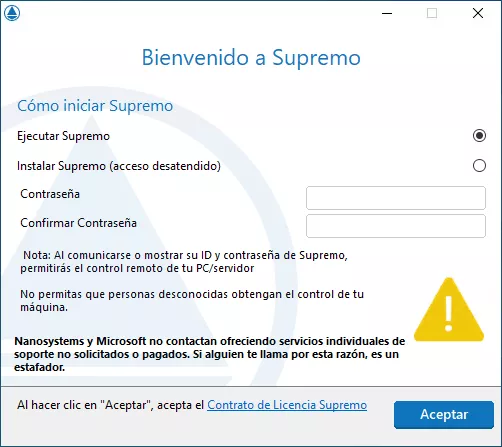
Phishing is a type of cyberattack that uses social engineering techniques to deceive victims and obtain confidential information such as login credentials, banking data, or personal information. Attackers impersonate companies, institutions, or trusted individuals to manipulate the user into clicking on a fraudulent link or downloading a malicious file.

Phishing Trends in 2025
Phishing attacks have evolved, and this year we see some concerning trends:
- AI-powered phishing : Cybercriminals use artificial intelligence to create extremely realistic emails and messages. AI bots can maintain real-time conversations to deceive the user.
- Deepfake phishing : the use of deepfake technology allows attackers to impersonate the voice and image of high-ranking company officials to deceive employees and obtain money transfers or critical data.
- Phishing through social networks: criminals use platforms like LinkedIn, Instagram, or WhatsApp to contact victims directly, impersonating colleagues or technical support.
- BEC (Business Email Compromise) attacks : fraudulent emails targeted at companies have become highly sophisticated, with personalized attacks that can cause significant financial losses.
How to Detect a Phishing Attempt
To avoid falling for these traps, it is important to recognize the most common signs:
- Grammatical and spelling errors : Fraudulent emails often contain mistakes that a legitimate company would not make.
- Suspicious email addresses : Check the sender’s address, as it often contains unusual domains.
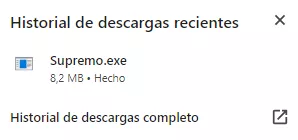
- Suspicious links : Hover over links to see their actual destination before clicking.
- Urgency messages : Cybercriminals create a sense of urgency to pressure you into acting quickly.
- Request for confidential information
How to Protect Yourself from Phishing
- Enable two-factor authentication (2FA) : Even if your password is stolen, without the second factor, attackers will not be able to access your accounts.
- Use advanced security tools: Cybersecurity solutions with real-time threat detection can help block malicious emails before they reach your inbox .
- Train your employees and collaborators : Cybersecurity training is key to reducing risks in the business environment.
- Always verify the source : If you receive a suspicious email, verify it directly with the purported sender before taking any action .
Conclusion
Phishing is a constantly evolving threat, and in 2025 it is more sophisticated than ever. Adopting preventive measures and using security tools can make the difference between protecting your information and becoming a victim of an attack.
Protect your business with advanced cybersecurity solutions. Contact us today and discover how we can help you strengthen your digital security. Contact us today and discover how we can help you strengthen your digital security.

FAQs
What is phishing?
Phishing is a cybercrime technique that seeks to deceive individuals into providing confidential information such as passwords or banking data by impersonating legitimate entities.
How can I identify a fraudulent email?
Phishing emails often contain grammatical or spelling errors, suspicious email addresses, misleading links, and urgency messages to prompt a quick reaction.
What types of phishing exist?
In addition to email phishing, there is "vishing" (fraudulent phone calls), "smishing" (deceptive text messages), and "quishing" (using QR codes to direct victims to fraudulent websites).
What should I do if I fall victim to a phishing attack?
Immediately change your passwords, contact the affected institutions, and monitor your accounts for any suspicious activity.
How can I protect myself from phishing?
Keep your software updated, enable two-factor authentication, avoid clicking on suspicious links, and educate yourself on cybersecurity best practices.
Are businesses targets for phishing?
Yes, companies are often targets of phishing attacks, especially through Business Email Compromise (BEC), where identities are impersonated to obtain confidential information or money transfers.
What is "quishing"?
"Quishing" is a form of phishing that uses QR codes to direct victims to fraudulent websites with the aim of stealing personal information or installing malicious software.
How can I verify the legitimacy of a suspicious email?
Check the sender's email address, look for grammatical or spelling errors, hover over links to see their actual destination, and if in doubt, contact the purported sender directly.